You can map attributes in the identity provider (IdP) response to custom attributes used in the Commvault software. For example, by default, a user email address is expected in the NameID element in the IdP response. If your IdP sends the user email address in an attribute instead of in the NameID element, you can map that attribute name to a custom attribute (for example, Email) so that the value of the attribute is used for the user email address.
Available Attributes
You can map IdP response attributes to the custom attributes in the following table. Your mappings take precedence over default sources.
|
Custom Attribute |
Description |
|---|---|
|
user name |
The mapping for the user name attribute is used to validate users when they log on. The default source for the user name attribute is the NameID element. |
|
user groups |
The mapping for the user groups attribute is used to associate or disassociate the user with domain groups (external groups) that were added to the Commvault environment. |
|
|
The mapping for the email attribute is used to validate the user when they log on. The default source for the email attribute is the NameID element. |
|
user GUID |
If the Auto create user option is selected, the mapping for the user GUID attribute is used as the user GUID. If the Auto create user option is selected and a mapping is not provided, the user GUID is a system-generated value. |
|
SID Group SID |
Applies to: Active Directory identity providers The mappings for the SID attribute and the group SID attribute are used to facilitate the access control list browse for agents such as the Windows File System Agent and the SharePoint Server Agent. |
|
company name |
Applies to: Multi-tenant Commvault environments The mapping for the company name attribute is used to configure SAML authentication at the CommCell level. The SAML authentication applies to all companies in the Commvault environment. |
Procedure
-
From the navigation pane, go to Manage > Security > Identity server.
The Identity servers page appears.
-
In the Application name column, click the application.
The application page appears.
-
Under Attribute mappings, click Edit.
The Edit attributes dialog box appears.
-
Click Add mappings.
-
Enter the attribute name based on the format in the IdP response:
-
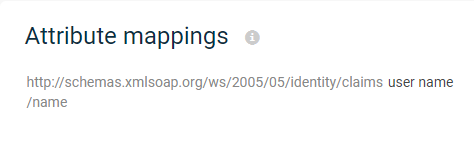
To add the attribute name using the URL format (for example, http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress), in the SAML attribute box, add the URL.
-
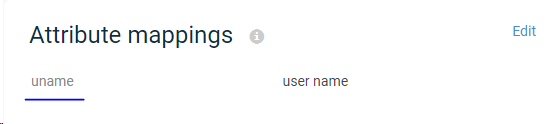
To add the attribute name using the generic name format (for example, uname), in the SAML attribute box, enter the name.
-
-
From the Custom attributes list, select the custom attribute to map the IdP response to.
For example, if the IdP response attribute is http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress, select Email.
-
To add additional mappings, click Add mappings.
Note
If you add a user name mapping, you must add an email mapping too.
-
Click Save.
Examples
The following are example mappings and the results of the mappings:
|
SAML Attribute |
Custom Attribute |
Attribute Statement |
Result |
|---|---|---|---|
|
user name |
|
The value |
|
|
|
The value |
|
user groups |
|
The user is associated with the |
|
company name |
|
|
Related Topics
For instructions about configuring SAML authentication at the CommCell level, see Configuring SAML Authentication for All Tenants .