Even after adopting the best practices of moving the information to a separate resource like Amazon Web Services, it is still important to protect the credentials as the newer forms of ransomware also extract credential information.
Some recommendations to protect credentials and reduce the attack envelope:
-
Lock away the AWS root keys
-
Make extensive use of account segmentation
-
Employ role based access controls within Commvault
-
Always grant the least privileges
-
Rotate credentials regularly
-
Remove unnecessary credentials
-
Monitor activity in both AWS and Commvault
Anticipate and Prevent AWS Cloud Attacks
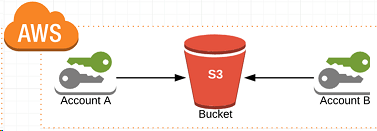
Account A Configuration
-
Commvault server w/AD account
-
Use S3 access/secret to access Account B’s bucket
Account B Configuration
-
Only accessible with a root account with FOB (Multi-Factor Authentication Device)
-
Only one S3 user with no IAM or ACL access
To be hacked from account A
-
Will need to compromise Active Directory
-
Will need to log on to Commvault server
-
Will need to manually delete jobs from Commvault
To be hacked from account B
-
Will need to steal both root account credentials and MFA device
-
Will need to steal S3 user credentials, then compromise account A, get into Commvault server, then access S3 endpoint of account A
-
Except this user has no right or ACL or IAM so it cannot change its own rights